North Korean Hackers Targeting Individuals: Report
North Korean Hackers Targeting Individuals: Report
"From a tradecraft perspective, the Lazarus Group now looks more like a criminal enterprise than a nation-state," Ryan Kalember, Proofpoint's senior vice president of cybersecurity strategy, told The Hill.
Active since at least 2009, the Lazarus Group is considered one of the most disruptive nation-state sponsored actors, accused of being involved in numerous high-profile attacks. Some of these include the 2014 Sony Pictures hack, last year’s theft of $81 million from the Bangladesh Bank, and this year’s WannaCry ransomware attack.
The Lazarus Group, an industry name for the believed-to-be North Korean hackers that breached Sony Pictures and launched the disastrous WannaCry malware, has already been linked to several different attempts to generate revenue by hacking. The group was tied to a string of bank robberies using the SWIFT interbank transfer request system totaling hundreds of millions of dollars, as well as recent attempts to phish cryptocurrency exchanges.
The multistage attacks that Proofpoint has uncovered rely on cryptocurrency-related lures to spread sophisticated backdoors and reconnaissance malware. In some cases, the hackers deploy additional malware, including the Gh0st remote access Trojan (RAT), in an attempt to steal credentials for cryptocurrency wallets and exchanges.
Proofpoint explains in a new report that Lazarus has started infecting South Korean credit card terminals, called point of sale (POS) systems, to steal credit card information.
The firm believes this would make North Korea the first known nation to steal credit cards this way.
Lazarus is also now no longer just phishing cryptocurrency exchanges, but also individuals who appear to own bitcoin and other digital currencies.
"As more people who are less technical start to invest in bitcoin, this could become more of a problem — and not just with Lazarus doing the stealing," said Kalember.
In a new report (PDF), Proofpoint details a new toolset associated with the Lazarus Group. Dubbed PowerRatankba, the toolset has been targeting individuals, companies, and organizations with interests in cryptocurrency via spear-phishing and phishing campaigns.
On Tuesday, the Trump administration blamed North Korea for the WannaCry malware that infected hundreds of thousands of systems in May. Such attributions from the executive branch have been extremely rare.
The report outlines two new pieces of malware being used by the group. Both are updates to the group's old malware, known as Ratankba.
RatankbaPOS, as the name suggests, is used in the POS robbery operations. PowerRatankba is like Ratankba but based in Power Shell, a Windows feature that runs commands.
Proofpoint linked the new attacks through shared code, idiosyncratic choices made during the programming and shared infrastructure with past Lazurus attacks.
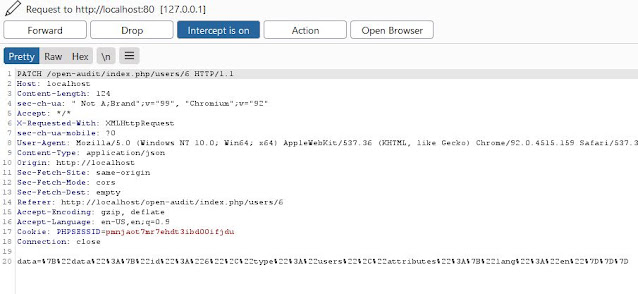
The hackers were observed using a total of six different attack vectors to deliver PowerRatankba, including a new Windows executable downloader called PowerSpritz, a malicious Windows Shortcut (LNK) file, malicious Compiled HTML Help (CHM) files, JavaScript (JS) downloaders, two macro-based Microsoft Office documents, and backdoored popular cryptocurrency applications hosted on internationalized domain (IDN) infrastructure, thus appearing as legitimate.
The campaigns started on or around June 30, 2017 and included highly targeted spear-phishing attacks focused on at least one executive at a cryptocurrency organization. While a PowerRatankba.A variant was used in these attacks, the rest of the campaigns used PowerRatankba.B, Proofpoint says
"We're as highly confident as we can be it's the same group," Kalember said.
/cdn.vox-cdn.com/uploads/chorus_image/image/57123343/shutterstock_498172096.0.jpg)





No comments